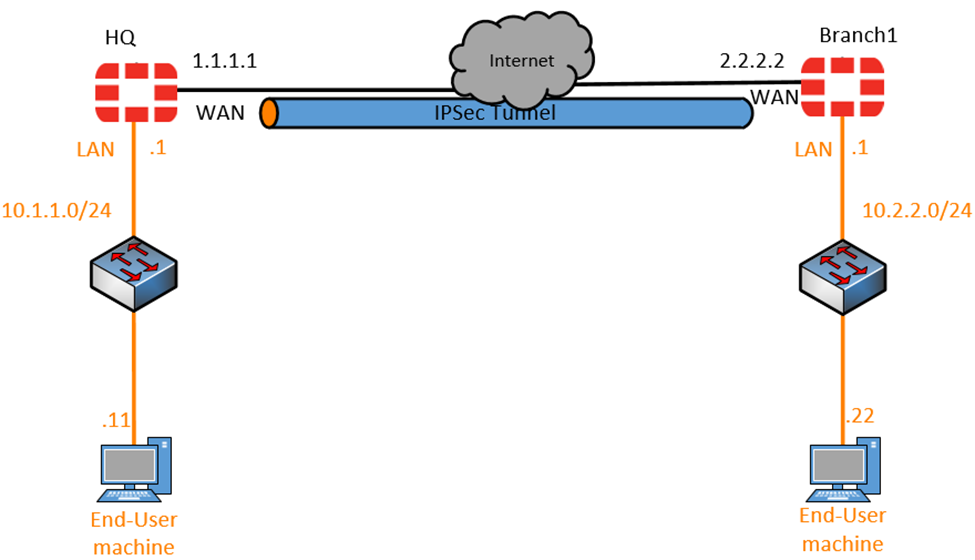
Site To Site Ipsec Vpn With Two Fortigates Fortigate This example shows you how to create a site to site ipsec vpn tunnel to allow communication between two networks that are located behind different fortigates. you use the vpn wizard’s site to site – fortigate template to create the vpn tunnel on both fortigates. in this example, one fortigate is called hq and the other is called branch. Here is the step by step guide on site a establish an ipsec vpn tunnel between both fortigates. add the multicast subnet 224.0.0.0 4 as a destination inside phase2 selectors. in this example, phase2 subnets are all to all: # config vpn ipsec phase1 interface edit "vpn sitea" set interface "port1" set proposal aes256 sha1 set dhgrp 5.

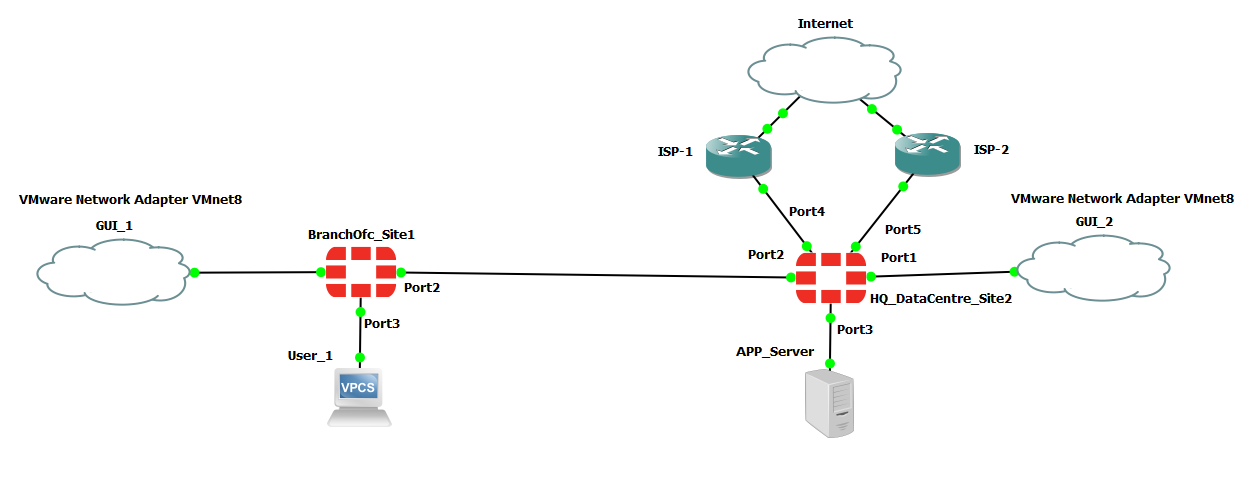
Site To Site Ipsec Vpn Between Two Fortigates Device вђ Network Configuring vpn between two fortigates using the default remote device type for site to site vpn. select name and nat configuration. vpn > ipsec wizard. enter the remote ip address and the outgoing interface as well as a pre shared key. select the local interface and subnets wanted to be connected as well as the remote subnet. In order to create an ipsec vpn tunnel on the fortigate device, select vpn > ipsec wizard and input the tunnel name. select the template type as site to site, the 'remote device type' as fortigate, and select nat configuration as no nat between sites. select 'next' to move to the authentication part. in the authentication step, set ip address. Go to vpn > ipsec wizard and select the custom template. enter the name vpn to hq and click next. for the ip address, enter the hq public ip address (172.25.176.142), and for interface, select the branch wan interface (wan1). for pre shared key, enter the matching secure key used in the vpn to branch tunnel. This video shows the steps to build a simple ipsec tunnel between two fortigates. i am using static routing to route traffic between the two sites in this de.
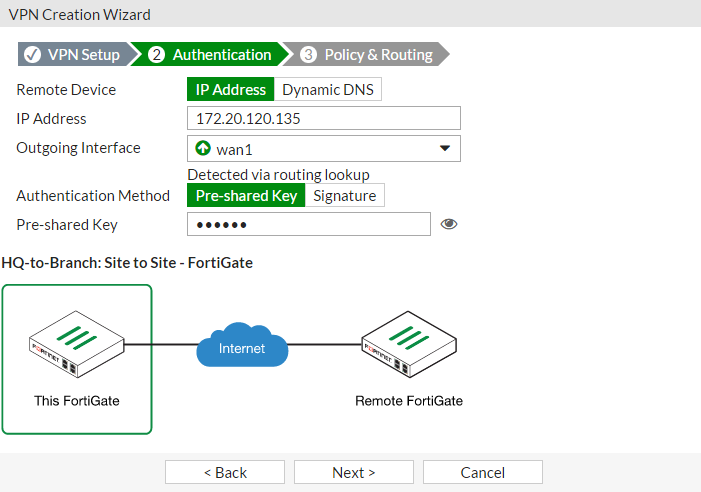
Site To Site Ipsec Vpn With Two Fortigates Go to vpn > ipsec wizard and select the custom template. enter the name vpn to hq and click next. for the ip address, enter the hq public ip address (172.25.176.142), and for interface, select the branch wan interface (wan1). for pre shared key, enter the matching secure key used in the vpn to branch tunnel. This video shows the steps to build a simple ipsec tunnel between two fortigates. i am using static routing to route traffic between the two sites in this de. A site to site vpn allows offices in multiple, fixed locations to establish secure connections with each other over a public network such as the internet. the following sections provide instructions for configuring site to site vpns: a site to site vpn connection lets branch offices use the internet to access the main office's intranet. a site. Configure the vpn setup. log into the fortigate firewall and go to vpn > ipsec wizard. name: hq to branch1. template type: site to site. nat configuration: no nat between sites. in our setup, both the branch1 and the headquarters are directly connected to the internet with public ip and no nat device in front.

Site To Site Ipsec Vpn Between Two Fortigates Device вђ Network A site to site vpn allows offices in multiple, fixed locations to establish secure connections with each other over a public network such as the internet. the following sections provide instructions for configuring site to site vpns: a site to site vpn connection lets branch offices use the internet to access the main office's intranet. a site. Configure the vpn setup. log into the fortigate firewall and go to vpn > ipsec wizard. name: hq to branch1. template type: site to site. nat configuration: no nat between sites. in our setup, both the branch1 and the headquarters are directly connected to the internet with public ip and no nat device in front.
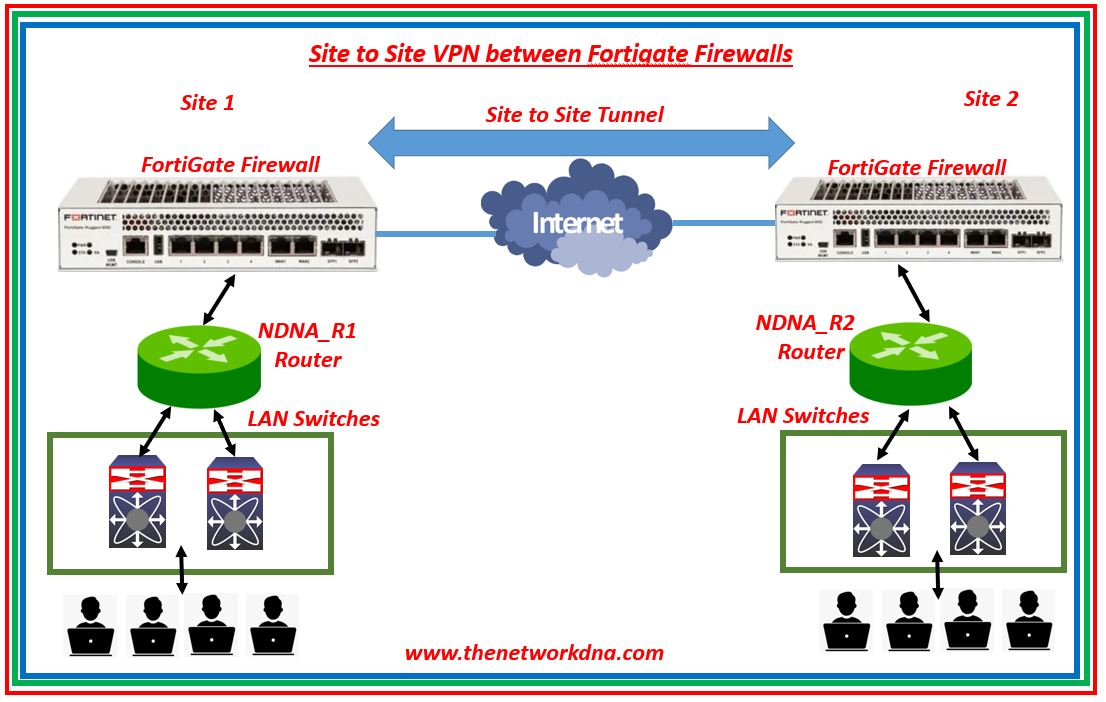
Site To Site Ipsec Vpn Tunnel With Two Fortigate Firewalls The
Site To Site Ipsec Vpn With Two Fortigates Fortigate
