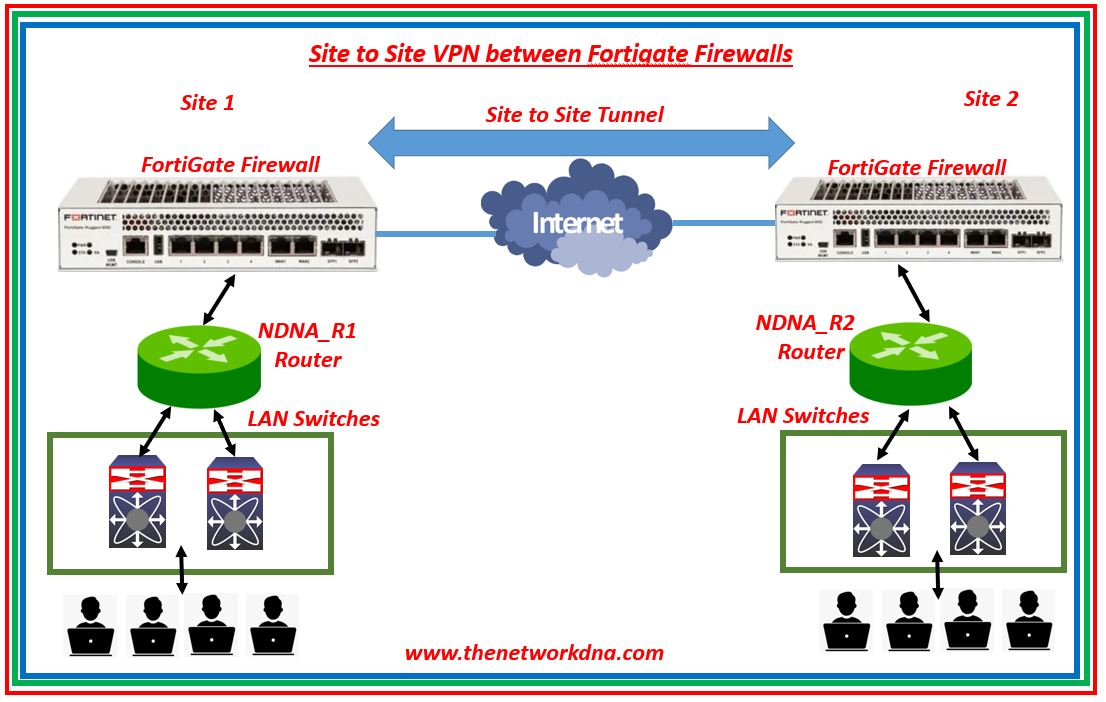
Site To Site Ipsec Vpn Tunnel With Two Fortigate Firewalls The Site to site ipsec vpn with two fortigates. this example shows you how to create a site to site ipsec vpn tunnel to allow communication between two networks that are located behind different fortigates. you use the vpn wizard’s site to site – fortigate template to create the vpn tunnel on both fortigates. In order to create an ipsec vpn tunnel on the fortigate device, select vpn > ipsec wizard and input the tunnel name. select the template type as site to site, the 'remote device type' as fortigate, and select nat configuration as no nat between sites. select 'next' to move to the authentication part. in the authentication step, set ip address.
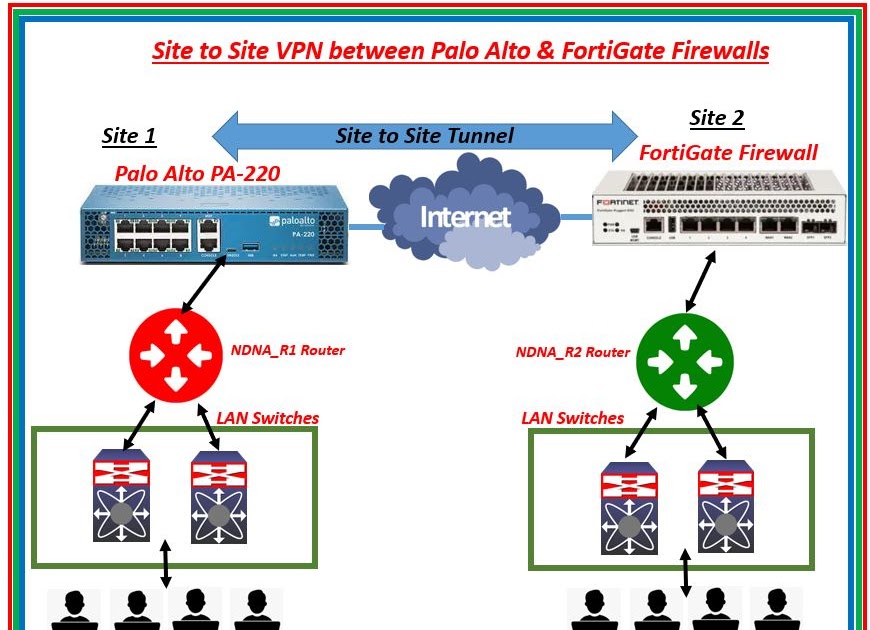
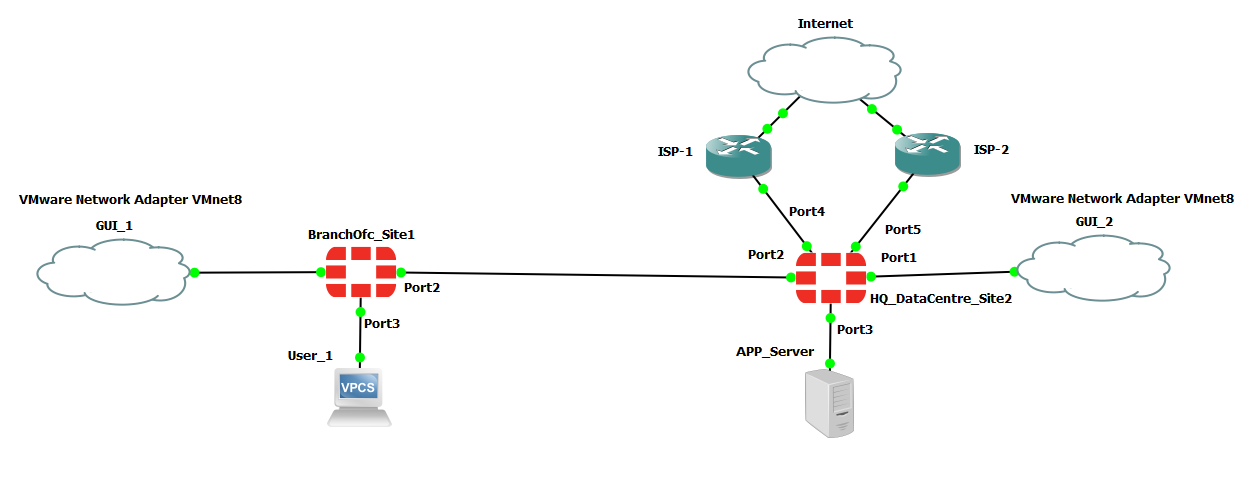
Ipsec Site To Site Vpn Tunnel Between Palo Alto Firewall Fort Configuring vpn between two fortigates using the default remote device type for site to site vpn. select name and nat configuration. vpn > ipsec wizard. enter the remote ip address and the outgoing interface as well as a pre shared key. select the local interface and subnets wanted to be connected as well as the remote subnet. Step 4: analyze the ike phase 1 messages on the responder for a solution. [phase 1 not up]. troubleshooting ike phase 1 problems is best handled by reviewing vpn status messages on the responder firewall. the responder is the 'receiver' side of the vpn that is receiving the tunnel setup requests. the initiator is the side of the vpn that sends. Configure multiple ipsec vpn tunnels on fortigate firewalls to secure work and home network.overview topology 0:00configure fortigate2 00:25configure for. Go to vpn > ipsec wizard and select the custom template. enter the name vpn to hq and click next. for the ip address, enter the hq public ip address (172.25.176.142), and for interface, select the branch wan interface (wan1). for pre shared key, enter the matching secure key used in the vpn to branch tunnel.
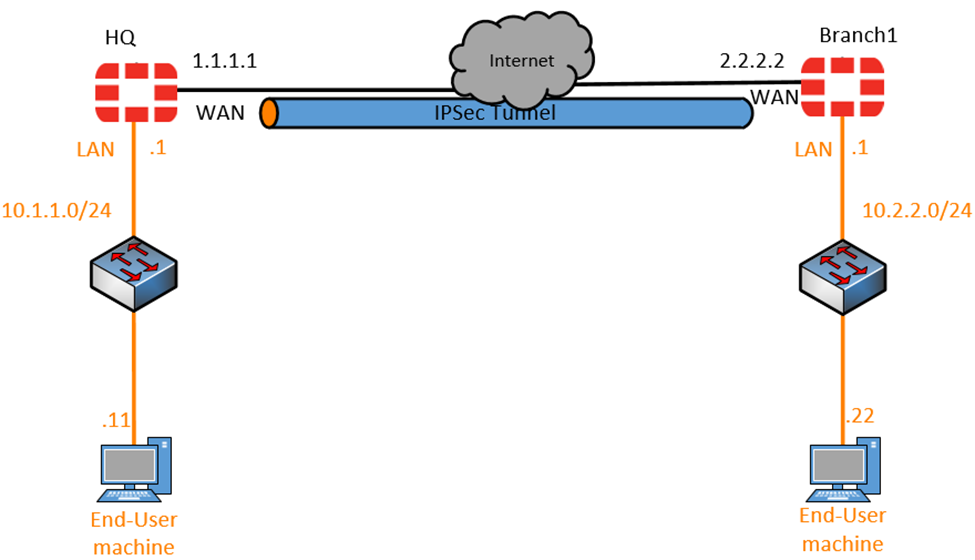
Site To Site Ipsec Vpn With Two Fortigates Fortigate Configure multiple ipsec vpn tunnels on fortigate firewalls to secure work and home network.overview topology 0:00configure fortigate2 00:25configure for. Go to vpn > ipsec wizard and select the custom template. enter the name vpn to hq and click next. for the ip address, enter the hq public ip address (172.25.176.142), and for interface, select the branch wan interface (wan1). for pre shared key, enter the matching secure key used in the vpn to branch tunnel. Configure the vpn setup. log into the fortigate firewall and go to vpn > ipsec wizard. name: hq to branch1. template type: site to site. nat configuration: no nat between sites. in our setup, both the branch1 and the headquarters are directly connected to the internet with public ip and no nat device in front. 1. configure phase1 of the ipsec tunnel in hq. we will start with the phase1 of the configuration and then we will proceed with the phase2. we are going to configure the phase1 of the tunnel with ikev2 and aes128 encryption algorithm and sha256 for the authentication. important things to keep in mind.

Site To Site Ipsec Vpn Between Two Fortigates Device вђ Network And Configure the vpn setup. log into the fortigate firewall and go to vpn > ipsec wizard. name: hq to branch1. template type: site to site. nat configuration: no nat between sites. in our setup, both the branch1 and the headquarters are directly connected to the internet with public ip and no nat device in front. 1. configure phase1 of the ipsec tunnel in hq. we will start with the phase1 of the configuration and then we will proceed with the phase2. we are going to configure the phase1 of the tunnel with ikev2 and aes128 encryption algorithm and sha256 for the authentication. important things to keep in mind.

Site To Site Ipsec Vpn Tunnel With Two Fortigate Firewalls The
Site To Site Ipsec Vpn With Two Fortigates Fortigate
