
Ipsec Tunnel Between Cisco Routers Site To Site Vpn Site to site ipsec vpn tunnels are used to allow the secure transmission of data, voice and video between two sites (e.g offices or branches). the vpn tunnel is created over the internet public network and encrypted using a number of advanced encryption algorithms to provide confidentiality of the data transmitted between the two sites. A site to site ipsec vpn tunnel is configured and established between the cisco rv series router at the remote office and the cisco 500 series isa at the main office. with this configuration, a host in lan 192.168.1.0 24 at the remote office and a host in lan 10.10.10.0 24 at the main office can communicate with each other securely over vpn.
How To Configure Site To Site Ipsec Vpn Tunnel In Cis Vrogue Co Hello justin. 1. this is a classic hub and spoke vpn topology as shown in attached schematic. 2. for traffic routing from site a to site c (and vice versa bidirectionally), via site b router thru the vpn tunnels established, you will need to configure the ipsec policy on each of the rv345 routers mentioned below. We will be using the example diagram above for the configuration scenario. generally, there are two phases for ipsec vpn: phase 1: in this phase we configure an isakmp policy. this policy establishes an initial secure channel over which further communication will follow. it defines how the ipsec peers will authenticate each other and what. Configurations. this document uses these configurations: router a. router b. note: cisco recommends that the acl applied to the crypto map on both the devices be a mirror image of each other. router a. ! . create an isakmp policy for phase 1 negotiations for the l2l tunnels. crypto isakmp policy 10. Step 6. check the vpn tunnel. check the availability of the vpn tunnel by pinging a device from the remote subnet. for example, send a ping request from a workstation at the main office to a server located at the branch office: r main#ping 192.168.20.10 type escape sequence to abort.
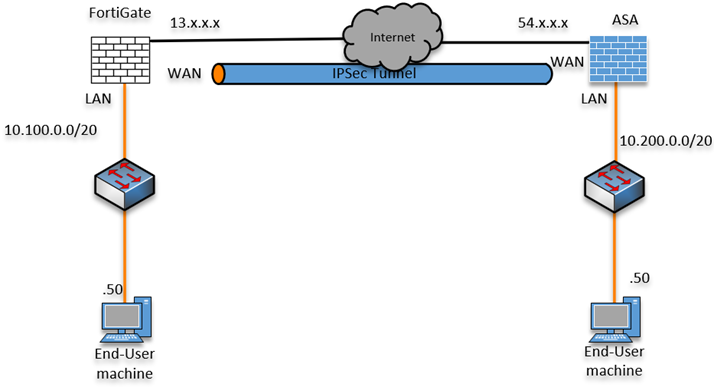
Ipsec Tunnel Between Cisco Routers Site To Site Vpn B Vrogue Co Configurations. this document uses these configurations: router a. router b. note: cisco recommends that the acl applied to the crypto map on both the devices be a mirror image of each other. router a. ! . create an isakmp policy for phase 1 negotiations for the l2l tunnels. crypto isakmp policy 10. Step 6. check the vpn tunnel. check the availability of the vpn tunnel by pinging a device from the remote subnet. for example, send a ping request from a workstation at the main office to a server located at the branch office: r main#ping 192.168.20.10 type escape sequence to abort. How ipsec works. ipsec involves many component technologies and encryption methods. yet ipsec's operation can be broken down into five main steps: 1. "interesting traffic" initiates the ipsec process. traffic is deemed interesting when the ipsec security policy configured in the ipsec peers starts the ike process.2. ike phase 1. Ipsec provides secure tunnels between two peers, such as two routers. you define which packets are considered sensitive and should be sent through these secure tunnels, and you define the parameters that should be used to protect these sensitive packets by specifying the characteristics of these tunnels.

Configuring Site To Site Ipsec Vpn Tunnel Between Cisco ођ How ipsec works. ipsec involves many component technologies and encryption methods. yet ipsec's operation can be broken down into five main steps: 1. "interesting traffic" initiates the ipsec process. traffic is deemed interesting when the ipsec security policy configured in the ipsec peers starts the ike process.2. ike phase 1. Ipsec provides secure tunnels between two peers, such as two routers. you define which packets are considered sensitive and should be sent through these secure tunnels, and you define the parameters that should be used to protect these sensitive packets by specifying the characteristics of these tunnels.
