
Site To Site Ipsec Vpn Tunnel Between Cisco Asa And Meraki Mx The Figure site to site ipsec shows the general layout of this vpn. site to site ipsec ¶ site a¶ start with configuring the tunnel and related settings on the firewall at site a. phase 1¶ to add a new ipsec phase 1: navigate to vpn > ipsec. click add p1. fill in the settings as described below. click save when complete. To set up site to site vpn: make sure that your ethernet interfaces, virtual routers, and zones are configured properly. for more information, see configure interfaces and zones. create your tunnel interfaces. ideally, put the tunnel interfaces in a separate zone, so that tunneled traffic can use different policy rules.
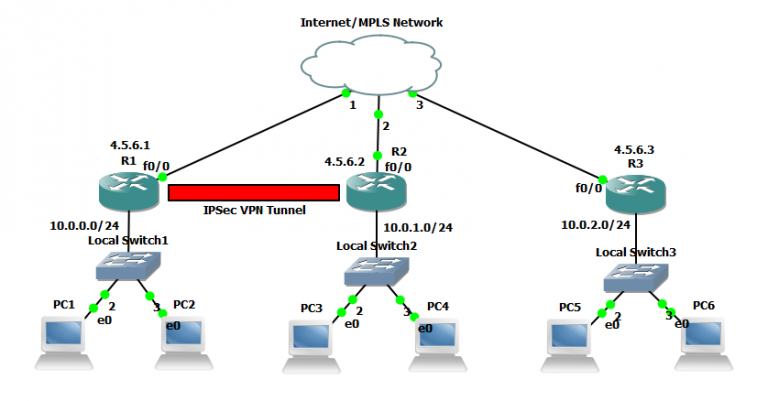
Configuring Ipsec Site To Site Vpn Tunnels With site to site vpn logs, you can gain access to details on ip security (ipsec) tunnel establishment, internet key exchange (ike) negotiations, and dead peer detection (dpd) protocol messages. for more information, see aws site to site vpn logs. available log formats: json, text. ike versions. the ike versions that are permitted for the vpn. Quick definition: an ipsec tunnel not only encrypts and authenticates the packets flowing through it, but it encapsulates each packet into an entirely new one, with a new header. this enables the creation of virtual private networks (vpns), which depend on ipsec tunnels for network to network, host to network and host to host communications. 10.1 and later. the ipsec tunnel configuration allows you to authenticate and or encrypt the data (ip packet) as it traverses the tunnel. ipsec tunnel mode is the default mode. ipsec tunnel mode creates a secure connection between two endpoints by encapsulating packets in an additional ip header. this means, in tunnel mode, the ipsec wraps the. These secure tunnels over the internet public network are encrypted using a number of advanced algorithms to provide confidentiality of data that is transmitted between multiple sites. this chapter explores how to configure routers to create a permanent secure site to site vpn tunnel. encryption will be provided by ipsec in concert with vpn.
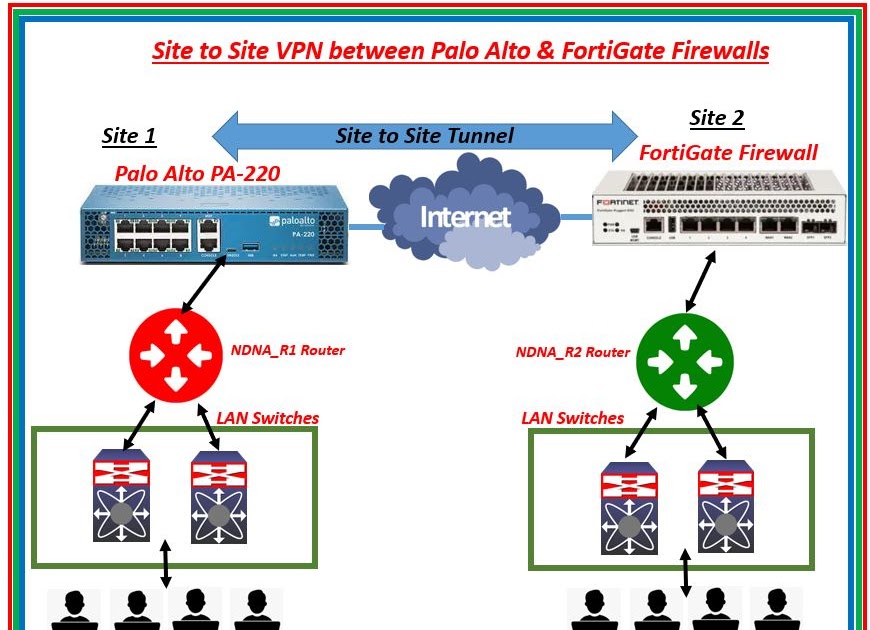
Ipsec Site To Site Vpn Tunnel Between Palo Alto Firewall Fortigate 10.1 and later. the ipsec tunnel configuration allows you to authenticate and or encrypt the data (ip packet) as it traverses the tunnel. ipsec tunnel mode is the default mode. ipsec tunnel mode creates a secure connection between two endpoints by encapsulating packets in an additional ip header. this means, in tunnel mode, the ipsec wraps the. These secure tunnels over the internet public network are encrypted using a number of advanced algorithms to provide confidentiality of data that is transmitted between multiple sites. this chapter explores how to configure routers to create a permanent secure site to site vpn tunnel. encryption will be provided by ipsec in concert with vpn. A site to site virtual private network (vpn) is a connection between two or more networks, such as a corporate network and a branch office network. organizations use site to site vpns to leverage an internet connection for private traffic as an alternative to private mpls circuits. site to site vpns are frequently used by companies with. How ipsec works. ipsec involves many component technologies and encryption methods. yet ipsec's operation can be broken down into five main steps: 1. "interesting traffic" initiates the ipsec process. traffic is deemed interesting when the ipsec security policy configured in the ipsec peers starts the ike process.2. ike phase 1.

Example Configuring A Site To Site Ipsec Vpn Tunnel Barracuda Campus A site to site virtual private network (vpn) is a connection between two or more networks, such as a corporate network and a branch office network. organizations use site to site vpns to leverage an internet connection for private traffic as an alternative to private mpls circuits. site to site vpns are frequently used by companies with. How ipsec works. ipsec involves many component technologies and encryption methods. yet ipsec's operation can be broken down into five main steps: 1. "interesting traffic" initiates the ipsec process. traffic is deemed interesting when the ipsec security policy configured in the ipsec peers starts the ike process.2. ike phase 1.
How To Configure Site To Site Ipsec Vpn Tunnel In Cis Vrogue Co
