
Ipsec Site To Site Vpn Tunnel Between Palo Alto Fire To set up site to site vpn: make sure that your ethernet interfaces, virtual routers, and zones are configured properly. for more information, see configure interfaces and zones. create your tunnel interfaces. ideally, put the tunnel interfaces in a separate zone, so that tunneled traffic can use different policy rules. 10.1 and later. the ipsec tunnel configuration allows you to authenticate and or encrypt the data (ip packet) as it traverses the tunnel. ipsec tunnel mode is the default mode. ipsec tunnel mode creates a secure connection between two endpoints by encapsulating packets in an additional ip header. this means, in tunnel mode, the ipsec wraps the.
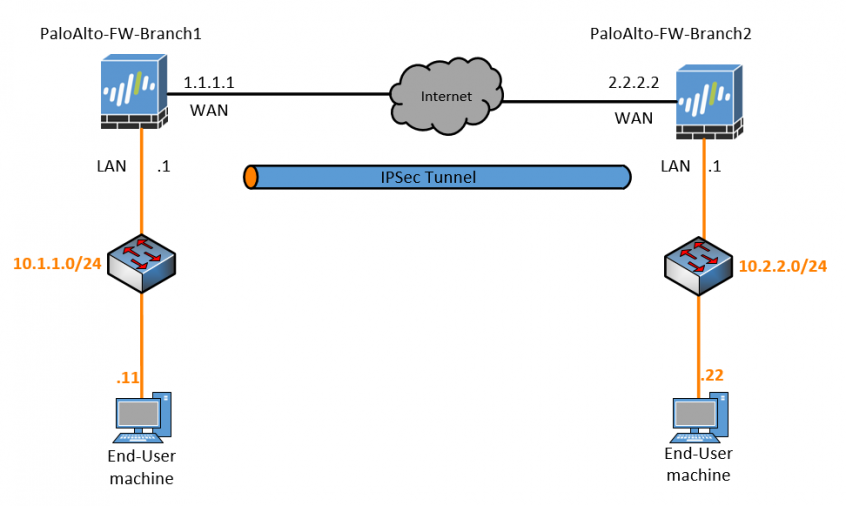
How To Configure Palo Alto Site To Site Vpn Using Ipsec вђ Getla We have 2 palo alot firewalls & we are trying to establish a ipsec tunnel between both. we proved that all vpn configurations are correct and were able to establish the tunnel & pass traffic but only if we add a firewall rule saying allow any any any any at the very top of the rule base, which goes against our security requirements. Select a security method for your vpn. in site to site vpn, the ipsec security method is used to create an encrypted tunnel from one customer network to a remote site of the customer. in remote access vpn, individual users are connected to the private network. decide on your vpn client. the site to site vpn does not need setup on each client. The problem in your configuration is that you route the peer ips to the tunnel interfaces. this way the firewalls try to reach these ips over an interface which has no connection at that time (the vpn connection is not established). the firewalls need to connect to the peer ips over the internet and not over the tunnel. Ipsec tunnel. select the tunnel interface, the ike gateway, and the ipsec crypto profile to make sure the proxy id is added, otherwise phase 2 will not come up. route. add the route of the internal network of the other side pointing towards the tunnel interface and select none: configuring cisco ip access list extended crypto acl.
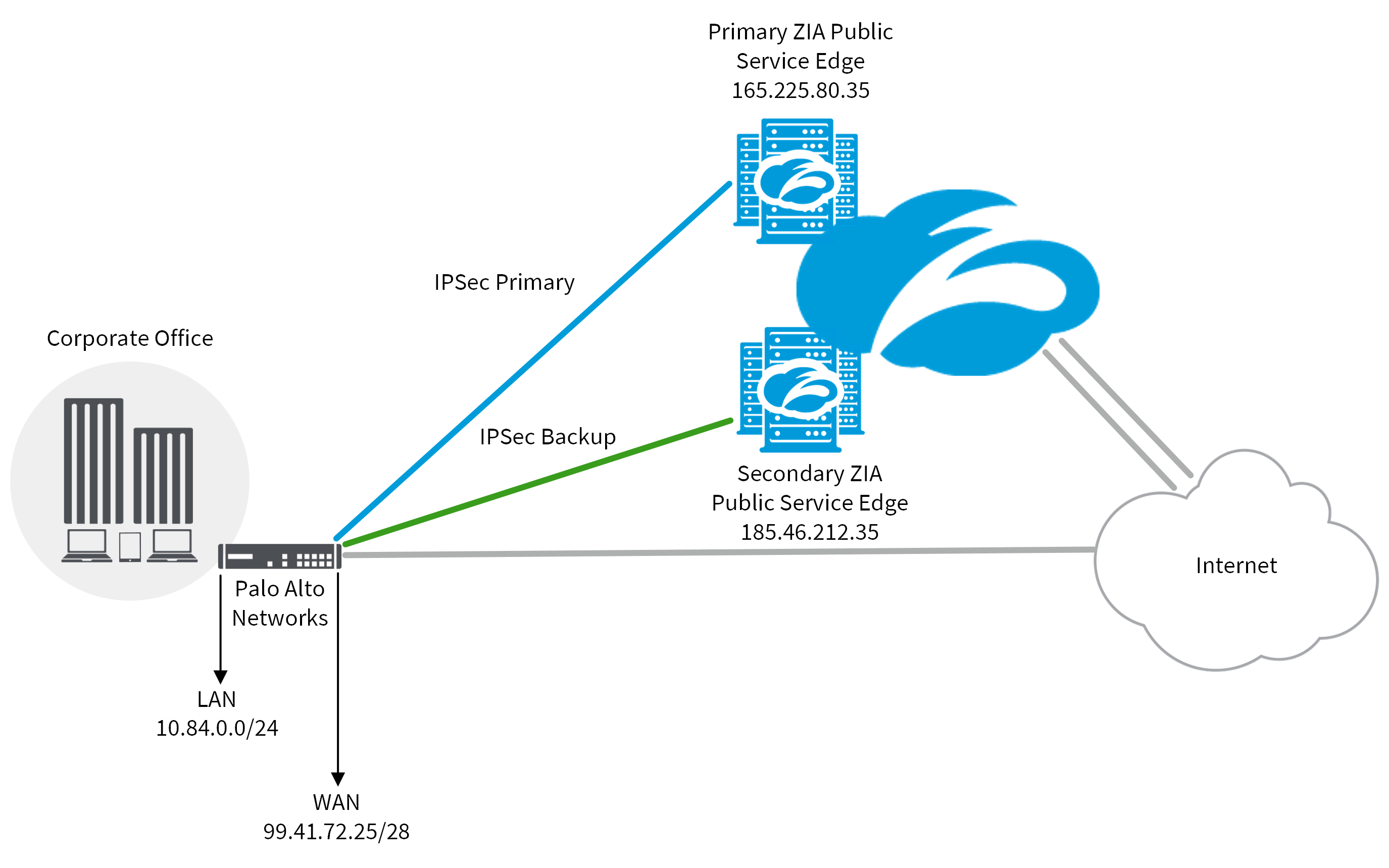
Ipsec Vpn Configuration Guide For Palo Alto Networks Firewall Zscaler The problem in your configuration is that you route the peer ips to the tunnel interfaces. this way the firewalls try to reach these ips over an interface which has no connection at that time (the vpn connection is not established). the firewalls need to connect to the peer ips over the internet and not over the tunnel. Ipsec tunnel. select the tunnel interface, the ike gateway, and the ipsec crypto profile to make sure the proxy id is added, otherwise phase 2 will not come up. route. add the route of the internal network of the other side pointing towards the tunnel interface and select none: configuring cisco ip access list extended crypto acl. If the vpn over isp 1 fails, then the secondary vpn tunnel through the secondary isp (isp2) will pass the traffic to the remote side. once the primary vpn tunnel recovers the traffic will fall back to the primary vpn tunnel. procedure. pa firewalls can only be configured for route based vpn tunnels. the concept of policy based site to site vpn. Step 5. under network > ipsec tunnels, click add to create a new ipsec tunnel. in the general window use the tunnel interface, the ike gateway and ipsec crypto profile from above to set up the parameters to establish ipsec vpn tunnels between firewalls. note: if the other side of the tunnel is a peer that supports policy based vpn, you must.

Configure Site To Site Ipsec Vpn Tunnel In Palo Alto Firew If the vpn over isp 1 fails, then the secondary vpn tunnel through the secondary isp (isp2) will pass the traffic to the remote side. once the primary vpn tunnel recovers the traffic will fall back to the primary vpn tunnel. procedure. pa firewalls can only be configured for route based vpn tunnels. the concept of policy based site to site vpn. Step 5. under network > ipsec tunnels, click add to create a new ipsec tunnel. in the general window use the tunnel interface, the ike gateway and ipsec crypto profile from above to set up the parameters to establish ipsec vpn tunnels between firewalls. note: if the other side of the tunnel is a peer that supports policy based vpn, you must.
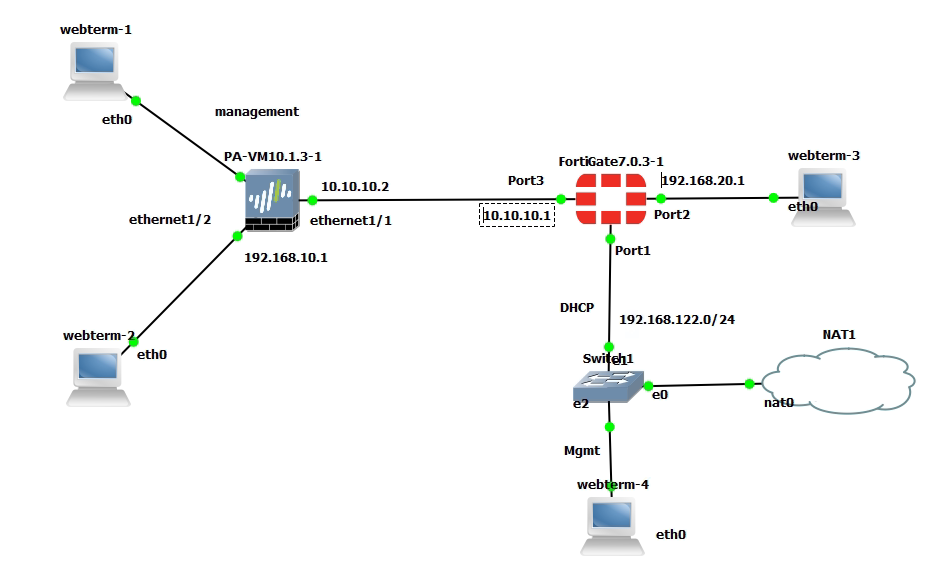
Create Ipsec Site To Site Vpn Between Palo Alto And F Vrog

Ipv6 Ipsec Vpn Tunnel Palo Alto Fortigate
