вїquг Es Una Ipsec Vpn Y Cгіmo Funciona Surfshark This video steps through the architecture of ipsec vpns. ipsec vpn negotiation occurs in two phases. in phase 1, participants establish a secure channel in w. This document will outline basic negotiation and configuration for crypto map based ipsec vpn configuration. this document is intended as an introduction to certain aspects of ike and ipsec, it will contain certain simplifications and colloquialisms. what is ipsec. ipsec is a standard based security architecture for ip hence ip sec.

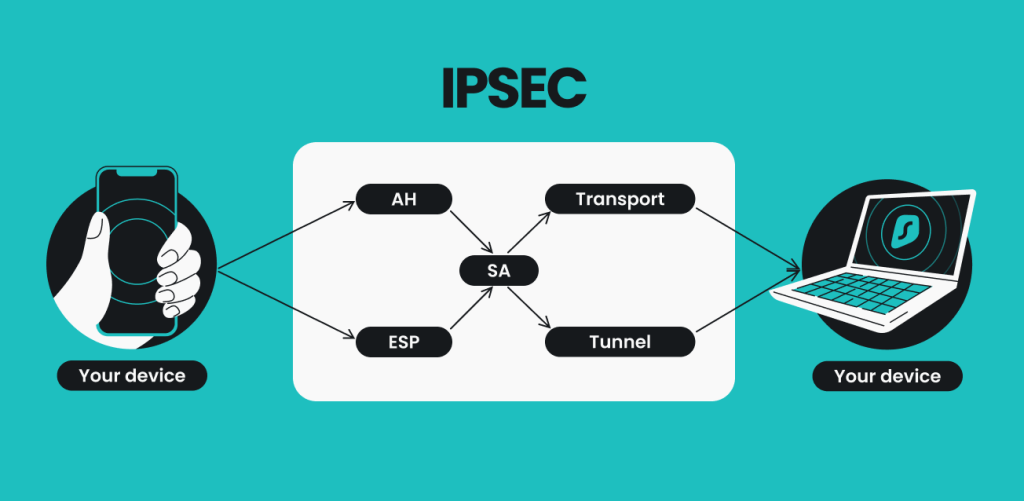
Ipsec Vpn Fundamentals Ipsec is a group of protocols for securing connections between devices. ipsec helps keep data sent over public networks secure. it is often used to set up vpns, and it works by encrypting ip packets, along with authenticating the source where the packets come from. within the term "ipsec," "ip" stands for "internet protocol" and "sec" for "secure.". Ipsec provides data confidentiality and integrity, including authentication, integrity check, and encryption. ipsec vpn is one of the two common vpn protocols, or sets of standards used to establish a vpn connection. at the ip layer, ipsec provides secure, remote access to an entire network (rather than just a single device). You will explore the fundamentals of ipsec vpn including encryption, authentication, key management and secure network connectivity. after completing this course you will be able to implement and troubleshoot ipsec vpns designs and issues in lab or production environment. you will also be prepared to follow industry standard and best practices. An ipsec vpn, or virtual private network, is a vpn that uses the ipsec protocol to create an encrypted tunnel on the internet. a vpn routes traffic along an encrypted tunnel, protecting data from unwanted intrusions. an ipsec vpn does this using the ipsec protocol to establish a connection and encrypt data packets in transit and is particularly.

Learn The Basics Of Ipsec Vpn Configuration You will explore the fundamentals of ipsec vpn including encryption, authentication, key management and secure network connectivity. after completing this course you will be able to implement and troubleshoot ipsec vpns designs and issues in lab or production environment. you will also be prepared to follow industry standard and best practices. An ipsec vpn, or virtual private network, is a vpn that uses the ipsec protocol to create an encrypted tunnel on the internet. a vpn routes traffic along an encrypted tunnel, protecting data from unwanted intrusions. an ipsec vpn does this using the ipsec protocol to establish a connection and encrypt data packets in transit and is particularly. The ipsec tunnel comes up only when there is an interesting traffic destined to the tunnel. to manually initiate the tunnel, check the tunnel status and clear tunnels by referring to troubleshooting site to site vpn issues using the cli. ike phase 1. —ike is a key management protocol standard used with ipsec. Description. this course provides a deep dive into the world of ipsec vpns and proxy, covering everything from basic concepts to advanced troubleshooting techniques. participants will gain a thorough understanding of ipsec, virtual private networks (vpn) & proxy, and their various types. the course delves into the inner workings of ipsec.

Crypto Map Based Ipsec Vpn Fundamentals Pdf Security Technology The ipsec tunnel comes up only when there is an interesting traffic destined to the tunnel. to manually initiate the tunnel, check the tunnel status and clear tunnels by referring to troubleshooting site to site vpn issues using the cli. ike phase 1. —ike is a key management protocol standard used with ipsec. Description. this course provides a deep dive into the world of ipsec vpns and proxy, covering everything from basic concepts to advanced troubleshooting techniques. participants will gain a thorough understanding of ipsec, virtual private networks (vpn) & proxy, and their various types. the course delves into the inner workings of ipsec.
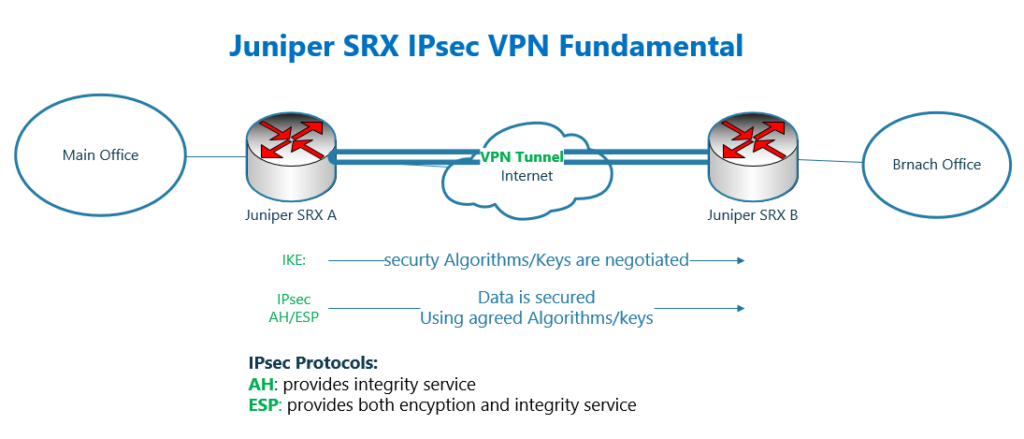
21 Juniper Srx Ipsec Vpn Fundamental Rayka Are You A Network Engineer
