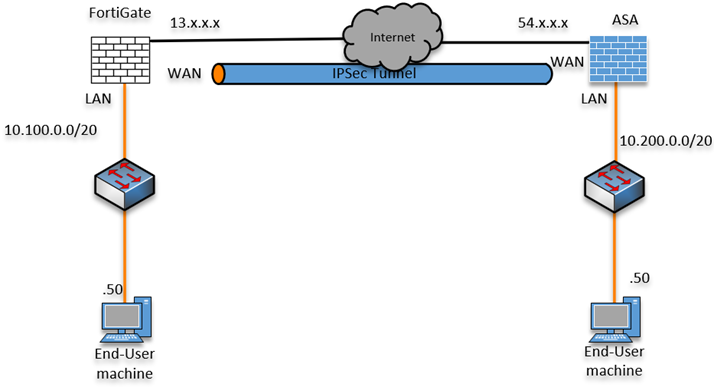
How To Set Up Ipsec Site To Site Vpn Between Fortigate And Asa Fortigate – i configuration. in order to create an ipsec vpn tunnel on the fortigate device, select vpn > ipsec wizard and input the tunnel name. select the template type as site to site, the 'remote device type' as fortigate, and select nat configuration as no nat between sites. select 'next' to move to the authentication part. From x0 to vpn: the tunnel should now be up and running. if not, go to fortigate, under dashboard > network, select ipsec, select the tunnel, and bring up phase 2. verification . make sure the tunnel is up by looking at the status on both side. fortigate: sonicwall: try to ping a host on the other side subnet from the fortigate and from the.
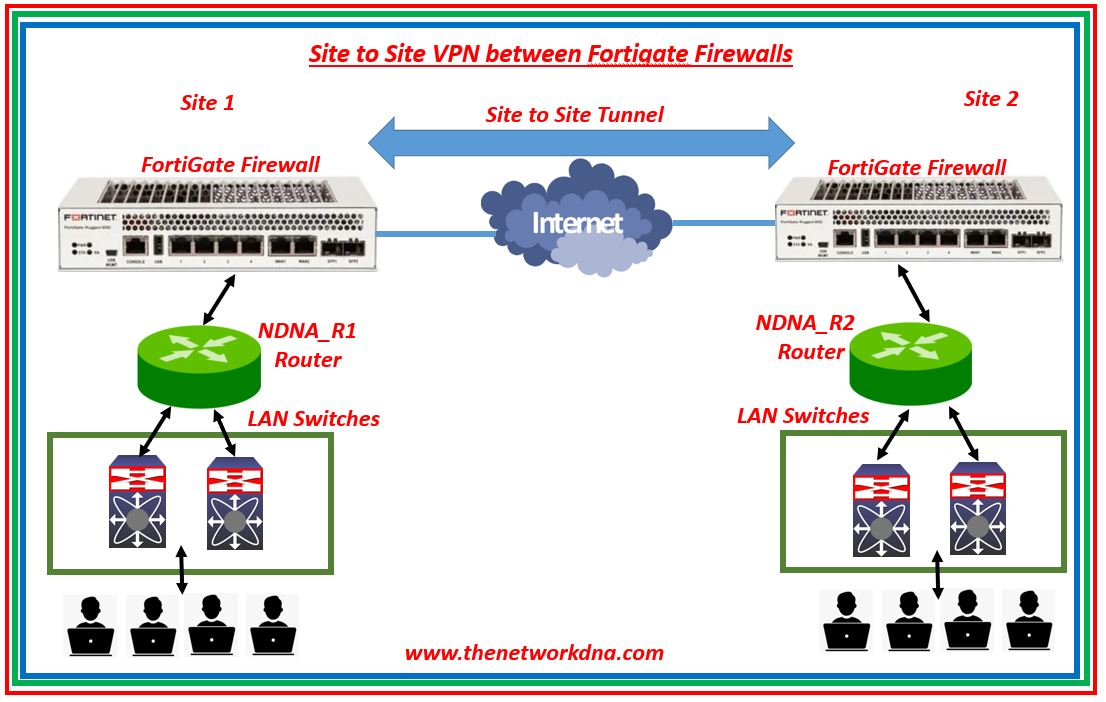
Site To Site Ipsec Vpn Tunnel With Two Fortigate Firewalls The Description. this article describes that this configuration example is a basic vpn setup between a fortigate unit and a cisco router, using a virtual tunnel interface (vti) on the cisco router. the ipsec configuration is only using a pre shared key for security. xauth or certificates should be considered for an added level of security. Site to site ipsec vpn with two fortigates. this example shows you how to create a site to site ipsec vpn tunnel to allow communication between two networks that are located behind different fortigates. you use the vpn wizard’s site to site – fortigate template to create the vpn tunnel on both fortigates. Configure the vpn setup. log into the fortigate firewall and go to vpn > ipsec wizard. name: hq to branch1. template type: site to site. nat configuration: no nat between sites. in our setup, both the branch1 and the headquarters are directly connected to the internet with public ip and no nat device in front. Configure multiple ipsec vpn tunnels on fortigate firewalls to secure work and home network.overview topology 0:00configure fortigate2 00:25configure for.
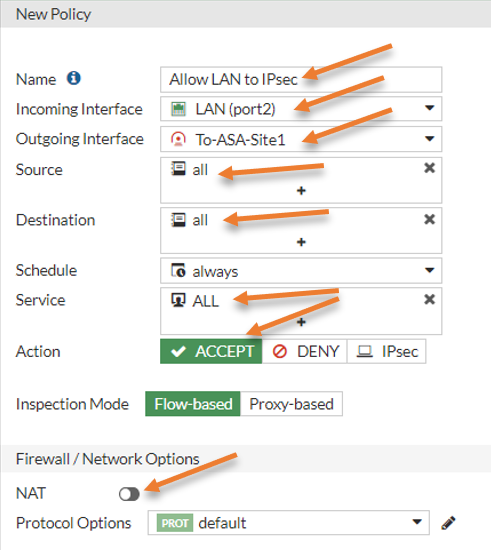
How To Set Up Ipsec Site To Site Vpn Between Fortigate And Asa Configure the vpn setup. log into the fortigate firewall and go to vpn > ipsec wizard. name: hq to branch1. template type: site to site. nat configuration: no nat between sites. in our setup, both the branch1 and the headquarters are directly connected to the internet with public ip and no nat device in front. Configure multiple ipsec vpn tunnels on fortigate firewalls to secure work and home network.overview topology 0:00configure fortigate2 00:25configure for. Remote gateway: static ip address. ip address: enter the public ip address of the asa firewall. interface: choose the outside interface of the fortigate firewall. local gateway: toggle the local gateway switch and choose primary ip. it will auto fill the outside ip address of the fortigate firewall. To configure ipsec vpn: go to vpn > ipsec wizard and select the custom template. enter the name vpn to branch and click next. for the ip address, enter the branch public ip address (172.25.177.46), and for interface, select the hq wan interface (wan1). for pre shared key, enter a secure key.
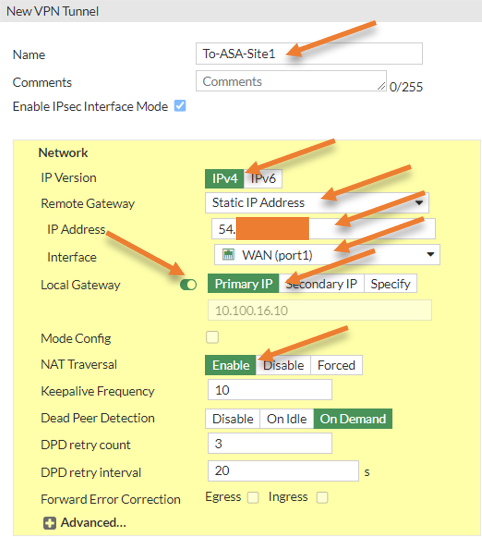
How To Set Up Ipsec Site To Site Vpn Between Fortigate And Asa Remote gateway: static ip address. ip address: enter the public ip address of the asa firewall. interface: choose the outside interface of the fortigate firewall. local gateway: toggle the local gateway switch and choose primary ip. it will auto fill the outside ip address of the fortigate firewall. To configure ipsec vpn: go to vpn > ipsec wizard and select the custom template. enter the name vpn to branch and click next. for the ip address, enter the branch public ip address (172.25.177.46), and for interface, select the hq wan interface (wan1). for pre shared key, enter a secure key.
