How To Configure Bgp Routing Over A Ikev1 Ipsec Vpn Tun Click send changes and activate. step 3. configure the site to site vpn settings. configure a site to site vpn ipsec tunnel including the vpn next hop interface. go to configuration > configuration tree > box > assigned services > vpn service > site to site. click lock. click the ipsec ikev1 tunnels tab. Go to configuration > configuration tree > box > assigned services > ospf rip bgp service > ospf rip bgp settings. click lock. in the left menu, click bgp router setup. click to add an entry to the networks list. enter a name. click ok. enter the network you want to propagate as the network prefix.
How To Configure Bgp Over An Ikev1 Ipsec Vpn To A Third Party ођ Step 3.5 add a filter setup for the second ipsec tunnel. to make the route over the first ipsec tunnel the preferred route, we will lengthen the as path of the second tunnel. in the left menu of the ospf rip bgp settings page, click filter setup ipv4. click lock. in the route map ipv4 filters section, click . the route maps ipv4 window opens. There are several options for running dynamic routing over ipsec site to site vpn. a gre tunnel in conjunction with ipsec would allow ospf or eigrp. and certainly would allow bgp. a newer approach (and a bit easier to configure) is vti tunnel. this would support ospf or eigrp or bgp. Solution. the 'ip' and 'remote ip' commands must be set for both tunnel interfaces (see diagram below). these ip addresses are used to terminate the tunnel ip connectivity in order to establish bgp (or ospf) neighboring. without these commands the tunnel endpoint is not running ip, hence bgp is not even trying to establish any tcp session. So considering the topology i would pick the first option, simply adding a static route in client machines into 10.0.0.0 24. if the remote resources aren't in the same ip range, you would need to add one route per resource.
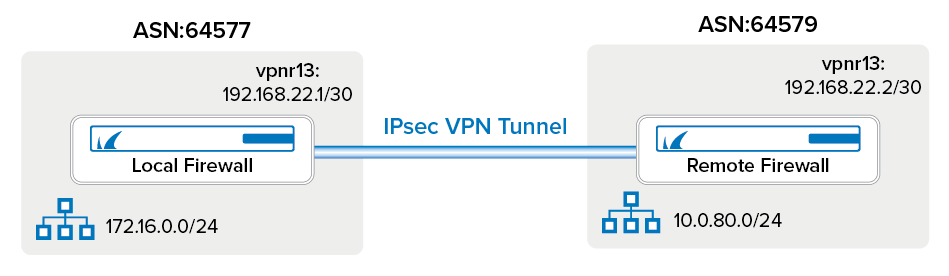
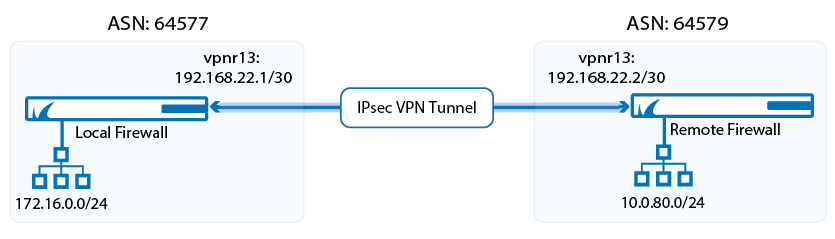
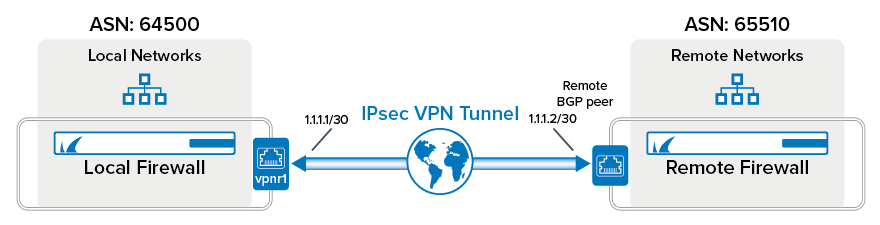
How To Configure Bgp Routing Over An Ikev1 Ipsec Vpn Tunnel Barracuda Solution. the 'ip' and 'remote ip' commands must be set for both tunnel interfaces (see diagram below). these ip addresses are used to terminate the tunnel ip connectivity in order to establish bgp (or ospf) neighboring. without these commands the tunnel endpoint is not running ip, hence bgp is not even trying to establish any tcp session. So considering the topology i would pick the first option, simply adding a static route in client machines into 10.0.0.0 24. if the remote resources aren't in the same ip range, you would need to add one route per resource. To set up site to site vpn: make sure that your ethernet interfaces, virtual routers, and zones are configured properly. for more information, see configure interfaces and zones. create your tunnel interfaces. ideally, put the tunnel interfaces in a separate zone, so that tunneled traffic can use different policy rules. Configure ipsec vpn. step 1. create a new point to point vpn topology. navigate to devices > vpn > site to site, and add a new firepower threat defense device vpn. step 2. configure ftd1 as one of the endpoints. object network ftd1 outside ip contains the outside interface ip address of the ftd1.
