Fortinet Vpn Ipsec Loceddis This article describes techniques on how to identify, debug and troubleshoot issues with ipsec vpn tunnels. scope. fortigate. solution . identification. as the first action, isolate the problematic tunnel. enter the vdom (if applicable) where the vpn is configured and type the command: get vpn ipsec tunnel summary. Create a geography based address object for the networks that can access the vpn: from the fortigate’s gui interface select: policy & object, addresses, click ‘create new’ then address. select type as 'geography', enter a name (e.g. allowed ip sec), set the interface to the external (wan) interface and select the country from the list.
Fortinet Vpn Ipsec Loceddis To add the peer id <local id>, open forticlient > edit the ipsec vpn tunnel (create new) > select advanced settings > select phase1 under vpn settings > enter local id. additionally, check the peer id by running the ike debug with the following commands: diagnose debug application ike 1. diagnose debug enable. This article describes a solution to set up vpns for loopback interfaces in fortios versions prior to v7.0.11. interface based ipsec was added in fortios v3.0. when this was first introduced, vrfs were not a feature, and the decision was made that if an ipsec interface is tied to a wan interface, the route lookup for esp in the ipsec layer. Configuring vpn between two fortigates using the default remote device type for site to site vpn. select name and nat configuration. vpn > ipsec wizard. enter the remote ip address and the outgoing interface as well as a pre shared key. select the local interface and subnets wanted to be connected as well as the remote subnet. Manually set: manual key configuration. if one of the vpn devices is manually keyed, the other vpn device must also be manually keyed with the identical authentication and encryption keys. enter the dns server ip, assign ip address, and subnet values. select the checkbox to enable split tunneling.
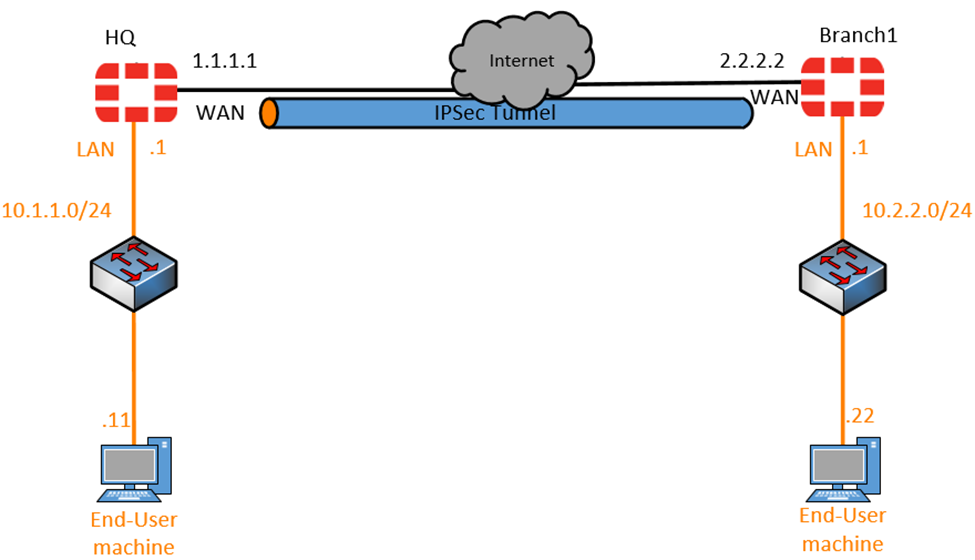
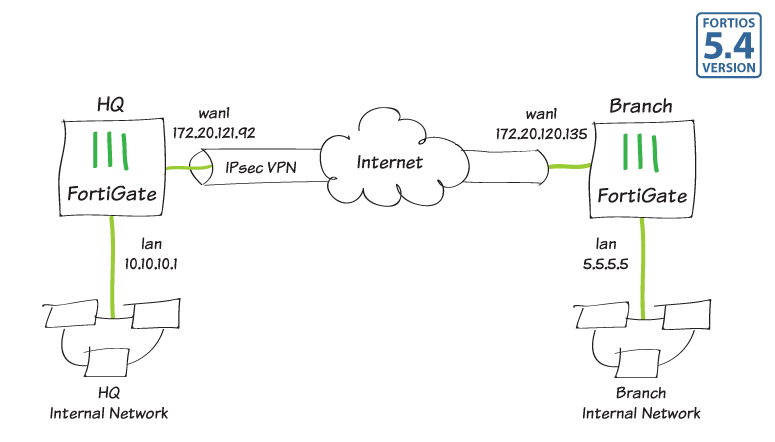
Site To Site Ipsec Vpn With Two Fortigates Fortigate Configuring vpn between two fortigates using the default remote device type for site to site vpn. select name and nat configuration. vpn > ipsec wizard. enter the remote ip address and the outgoing interface as well as a pre shared key. select the local interface and subnets wanted to be connected as well as the remote subnet. Manually set: manual key configuration. if one of the vpn devices is manually keyed, the other vpn device must also be manually keyed with the identical authentication and encryption keys. enter the dns server ip, assign ip address, and subnet values. select the checkbox to enable split tunneling. This article provides a configuration example for ipsec vpn tunnels between two fortigate in transparent mode (tp) on different subnets, as well as some troubleshooting steps. scope. all fortios 3.0 and 4.0. diagram. the following network scenario is used to illustrate this example : expectations, requirements. 7.4.5. ipsec vpn load balancing. ipsec vpn load balancing. the fortigate 6000f uses slbc load balancing to select an fpc to terminate traffic for a new ipsec vpn tunnel instance and all traffic for that tunnel instance is terminated on the same fpc. config vpn ipsec phase1 interface. edit <name>.
