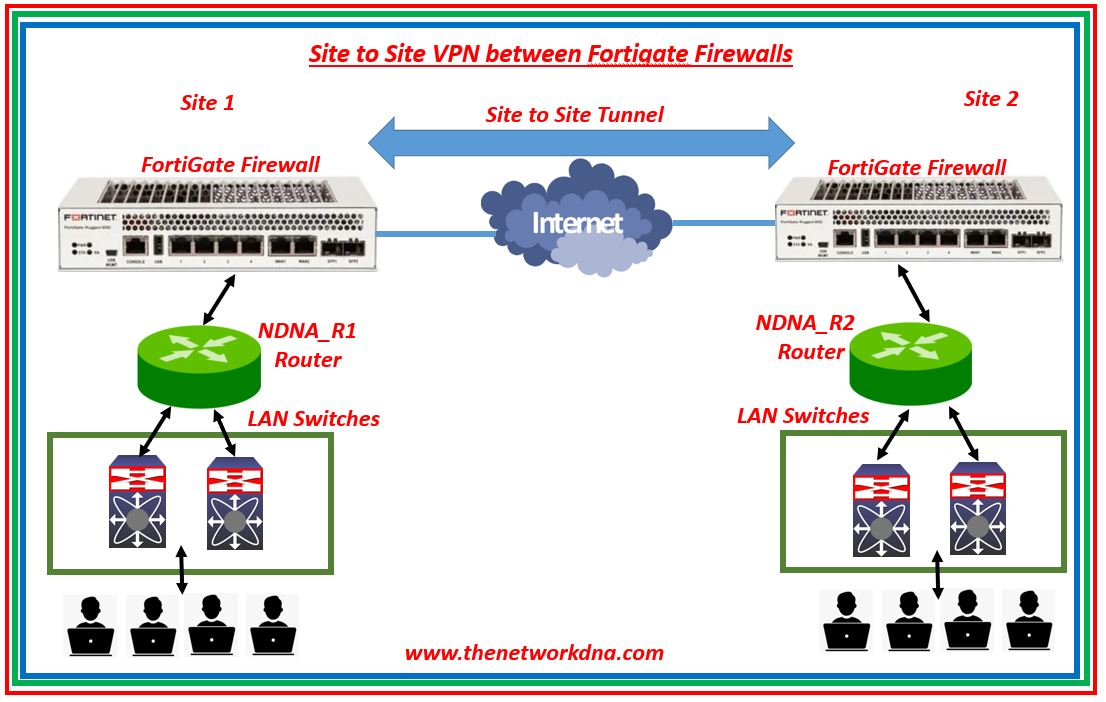
Site To Site Ipsec Vpn Tunnel With Two Fortigate Firewalls The Description. this article explains how a route based vpn interoperates with a policy based vpn. scope. any currently supported version of fortigate. solution. consider a scenario where the goal is to connect the following routed vpn and policy vpn through an ipsec tunnel: user a = 192.168.40.2, port9. user b = 192.168.41.2, port5. When it comes to remote work, vpn connections are a must. but they come in multiple shapes and sizes. join firewalls network engineer matt as he shows yo.

Fortigate Ipsec Vpn Configuration Guide This article discusses route based ipsec site to site redundant vpn failover using bgp. assign tunnel interface ip for both sites tunnel. configure bgp on both sites. set weight for neighbors as required. check the routing table. vpn tunnel with higher weight bgp neighbor will get priority. when tunnel vpn 2 goes down traffic will be forwarded. Configuring vpn between two fortigates using the default remote device type for site to site vpn. select name and nat configuration. vpn > ipsec wizard. enter the remote ip address and the outgoing interface as well as a pre shared key. select the local interface and subnets wanted to be connected as well as the remote subnet. This is my setup for this tutorial: (yes, public ipv4 addresses behind the forti.) i am using a fortinet fortiwifi fwf 61e with fortios v6.2.5 build1142 (ga) and a cisco asa 5515 with version 9.12 (3)12 and asdm 7.14 (1). these are the vpn parameters: route based vpn, that is: numbered tunnel interface and real route entries for the network (s. To learn how to configure ipsec tunnels, refer to the ipsec vpns section. after you have configured the ipsec tunnels, go to vpn > ipsec tunnels to verify the ipsec tunnels. in our example, we have two interfaces internet a (port1) and internet b (port5) on which we have configured ipsec tunnels branch hq a and branch hq b respectively.

Fortinet How To Setup A Route Based Ipsec Vpn Tunnel On A This is my setup for this tutorial: (yes, public ipv4 addresses behind the forti.) i am using a fortinet fortiwifi fwf 61e with fortios v6.2.5 build1142 (ga) and a cisco asa 5515 with version 9.12 (3)12 and asdm 7.14 (1). these are the vpn parameters: route based vpn, that is: numbered tunnel interface and real route entries for the network (s. To learn how to configure ipsec tunnels, refer to the ipsec vpns section. after you have configured the ipsec tunnels, go to vpn > ipsec tunnels to verify the ipsec tunnels. in our example, we have two interfaces internet a (port1) and internet b (port5) on which we have configured ipsec tunnels branch hq a and branch hq b respectively. To create the fortigate static route: in the fortigate, go to network > static routes. create an ipv4 static route that forces outgoing traffic going to azure to go through the route based tunnel. set the administrative distance to a value lower than the existing default route value. to create the azure site to site vpn connection:. Learn how to configure the ipsec vpn on your fortigate device with this cookbook from the fortinet documentation library. follow the step by step instructions and examples to set up a secure vpn connection.
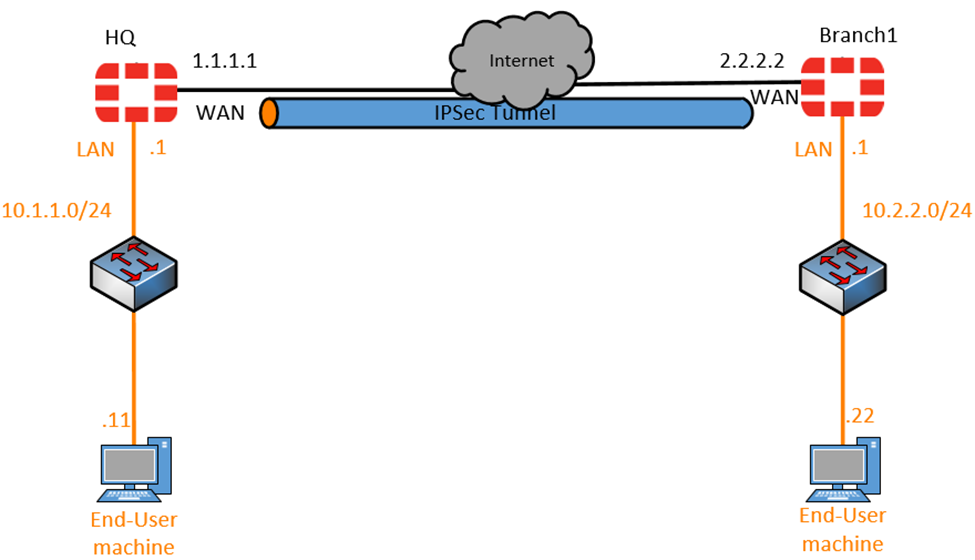
How To Configure Ipsec Site To Site Vpn On Fortigate Firewall To create the fortigate static route: in the fortigate, go to network > static routes. create an ipv4 static route that forces outgoing traffic going to azure to go through the route based tunnel. set the administrative distance to a value lower than the existing default route value. to create the azure site to site vpn connection:. Learn how to configure the ipsec vpn on your fortigate device with this cookbook from the fortinet documentation library. follow the step by step instructions and examples to set up a secure vpn connection.
