
Example Configuring A Site To Site Ipsec Vpn Tunnel Barracuda Campus To configure a site to site vpn connection between two barracuda nextgen x series firewalls, in which one unit (location 1) has a dynamic internet connection and the peer unit (location 2) has a static public ip address, create an ipsec tunnel on both units. in this setup, location 1 acts as the active peer. you will need to add an access rule. Step 3. create an ipsec tunnel on the remote appliance. configure the remote firewall or third party vpn gateway with the same settings. only the local and remote networks and the ip address for the remote vpn gateway must be interchanged. step 4. create access rules for vpn traffic. to allow traffic in and out of the vpn tunnel, create a pass.
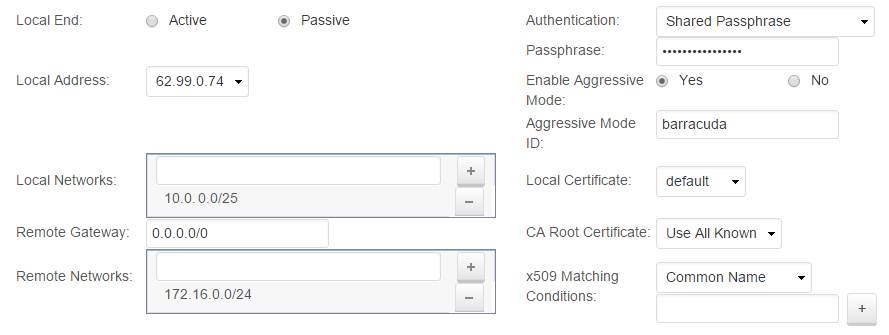
Example Configuring A Site To Site Ipsec Vpn Tunnel Barracuda Campus Create the ipsec tunnel on location 1. configure the x series firewall at location 1 with the dynamic wan ip as the active peer. log into the x series firewall at location 1. go to the vpn > site to site vpn page. in the site to site ipsec tunnels section, click add. enter a name for the vpn tunnel. configure the settings for phase 1 and phase 2. Hello, i need help to setup a s2s vpn tunnel using ikev2 between asa and barracuda firewall. please find the barracuda configuration attached below. this is my config on the asa which is not working: ! crypto ikev2 policy 60 encryption aes 256. To set up site to site vpn: make sure that your ethernet interfaces, virtual routers, and zones are configured properly. for more information, see configure interfaces and zones. create your tunnel interfaces. ideally, put the tunnel interfaces in a separate zone, so that tunneled traffic can use different policy rules. To establish a lan to lan connection, two attributes must be set: – connection type – ipsec lan to lan. – authentication method for the ip – in this scenario we will use preshared key for ikev2. the name of the tunnel is the ip address of the peer. ikev2 preshared key is configured as 32fjsk0392fg.
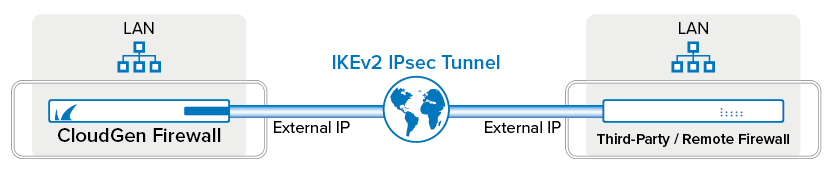
How To Configure A Site To Site Ipsec Ikev2 Vpn Tunnel Barracuda To set up site to site vpn: make sure that your ethernet interfaces, virtual routers, and zones are configured properly. for more information, see configure interfaces and zones. create your tunnel interfaces. ideally, put the tunnel interfaces in a separate zone, so that tunneled traffic can use different policy rules. To establish a lan to lan connection, two attributes must be set: – connection type – ipsec lan to lan. – authentication method for the ip – in this scenario we will use preshared key for ikev2. the name of the tunnel is the ip address of the peer. ikev2 preshared key is configured as 32fjsk0392fg. How ipsec works. ipsec involves many component technologies and encryption methods. yet ipsec's operation can be broken down into five main steps: 1. "interesting traffic" initiates the ipsec process. traffic is deemed interesting when the ipsec security policy configured in the ipsec peers starts the ike process.2. ike phase 1. Create phase1 using policy mode ipsec. 2. create phase2 in the phase2 configuration the source subnet must refer to the nat ip address since the traffic will be nated before entering the tunnel. quick mode selector must allow the traffic after nat has been applied.
