
Ipsec Site To Site Vpn Tunnel Between Palo Alto Firewall F To set up site to site vpn: make sure that your ethernet interfaces, virtual routers, and zones are configured properly. for more information, see configure interfaces and zones. create your tunnel interfaces. ideally, put the tunnel interfaces in a separate zone, so that tunneled traffic can use different policy rules. 2015 01 26 fortinet, ipsec vpn, palo alto networks fortigate, fortinet, ipsec, palo alto networks, site to site vpn johannes weber. this is a small tutorial for configuring a site to site ipsec vpn between a palo alto and a fortigate firewall. i am publishing step by step screenshots for both firewalls as well as a few troubleshooting cli commands.
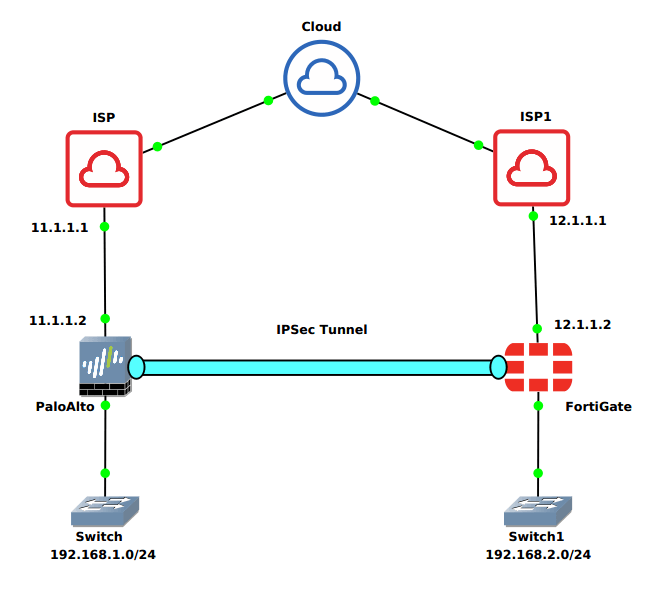
How To Configure Ipsec Vpn Between Palo Alto And Fortigate Firewall 10.1 and later. the ipsec tunnel configuration allows you to authenticate and or encrypt the data (ip packet) as it traverses the tunnel. ipsec tunnel mode is the default mode. ipsec tunnel mode creates a secure connection between two endpoints by encapsulating packets in an additional ip header. this means, in tunnel mode, the ipsec wraps the. In this video i will demonstrate how to configure site to site ipsec vpn tunnel between 2 palo alto firewalls.for feedback suggestions, please contact me at:. We have 2 palo alot firewalls & we are trying to establish a ipsec tunnel between both. we proved that all vpn configurations are correct and were able to establish the tunnel & pass traffic but only if we add a firewall rule saying allow any any any any at the very top of the rule base, which goes against our security requirements. A vpn connection that allows you to connect two local area networks (lans) is called a site to site vpn. you can configure route based vpns to connect palo alto networks firewalls located at two sites or to connect a palo alto networks firewall with a third party security device at another location. the firewall can also interoperate with third.
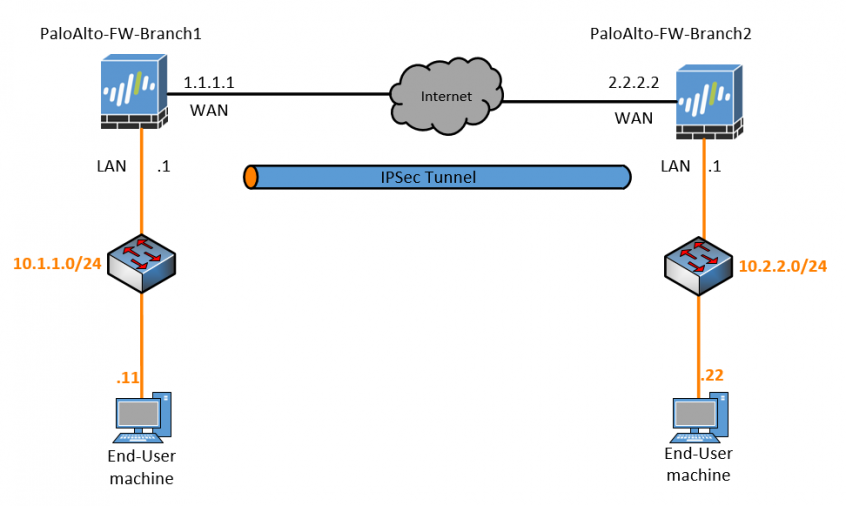
How To Configure Palo Alto Site To Site Vpn Using Ipsec вђ Getla We have 2 palo alot firewalls & we are trying to establish a ipsec tunnel between both. we proved that all vpn configurations are correct and were able to establish the tunnel & pass traffic but only if we add a firewall rule saying allow any any any any at the very top of the rule base, which goes against our security requirements. A vpn connection that allows you to connect two local area networks (lans) is called a site to site vpn. you can configure route based vpns to connect palo alto networks firewalls located at two sites or to connect a palo alto networks firewall with a third party security device at another location. the firewall can also interoperate with third. Fortigate, palo alto. go to: vpn > ipsec tunnels, select 'create new ' > ipsec tunnel. set the tunnel name (after creation, the tunnel name cannot be modified). the process is straightforward. using only one screen, it will be possible to configure phase 1 and phase 2. Step 5. under network > ipsec tunnels, click add to create a new ipsec tunnel. in the general window use the tunnel interface, the ike gateway and ipsec crypto profile from above to set up the parameters to establish ipsec vpn tunnels between firewalls. note: if the other side of the tunnel is a peer that supports policy based vpn, you must.
