
Ipsec Tunnel Between Cisco Routers Site To Site Vpn Configurations. this document uses these configurations: router a. router b. note: cisco recommends that the acl applied to the crypto map on both the devices be a mirror image of each other. router a. ! . create an isakmp policy for phase 1 negotiations for the l2l tunnels. crypto isakmp policy 10. To help make this an easy to follow exercise, we have split it into two steps that are required to get the site to site ipsec vpn tunnel to work. these steps are: (1) configure isakmp (isakmp phase 1) (2) configure ipsec (isakmp phase 2, acls, crypto map) our example setup is between two branches of a small company, these are site 1 and site 2.

Basic Ipsec Vpn Site To Site On Cisco Router Step By Step 01 You In this post we will describe briefly a lan to lan ipsec vpn and provide a full configuration example with two cisco ios routers using ipsec. have in mind also that site to site ipsec vpn can also be configured on cisco asa firewalls as i have described here. with ipsec vpns, businesses can connect together remote office lans over the internet. How ipsec works. ipsec involves many component technologies and encryption methods. yet ipsec's operation can be broken down into five main steps: 1. "interesting traffic" initiates the ipsec process. traffic is deemed interesting when the ipsec security policy configured in the ipsec peers starts the ike process.2. ike phase 1. Before you start configuring the ipsec vpn, make sure both routers can reach each other. i have already verified that both routers can ping each other so let’s start the vpn configuration. step 1. configuring ipsec phase 1 (isakmp policy) r1(config)#crypto isakmp policy 5. r1(config isakmp)#hash sha. This section describes the commands that you can use on the asa or cisco ios xe in order to verify the details for both phases 1 and 2. enter the show vpn sessiondb command on the asa for verification: ciscoasa# show vpn sessiondb detail l2l filter ipaddress 172.17.1.1. session type: lan to lan detailed.

Configuring Site To Site Ipsec Vpn Tunnel Between Cisco Routers Before you start configuring the ipsec vpn, make sure both routers can reach each other. i have already verified that both routers can ping each other so let’s start the vpn configuration. step 1. configuring ipsec phase 1 (isakmp policy) r1(config)#crypto isakmp policy 5. r1(config isakmp)#hash sha. This section describes the commands that you can use on the asa or cisco ios xe in order to verify the details for both phases 1 and 2. enter the show vpn sessiondb command on the asa for verification: ciscoasa# show vpn sessiondb detail l2l filter ipaddress 172.17.1.1. session type: lan to lan detailed. The router does this by default. in order to do this, when you define the trustpoint under the crypto map add the chain keyword as shown here: crypto map outside map 1 set trustpoint ios ca chain. if this is not done, then the the tunnel only gets negotiated as long as the asa is the responder. In this article, we configured ipsec vpn on cisco routers. we discussed the requirements for the ipsec vpn. after, we configure phase1 and phase2 on cisco router r1. the same configuration is done on the cisco router r2. you must need the static routable ip address to establish an ipsec tunnel between both the routers. hope you like this article!.
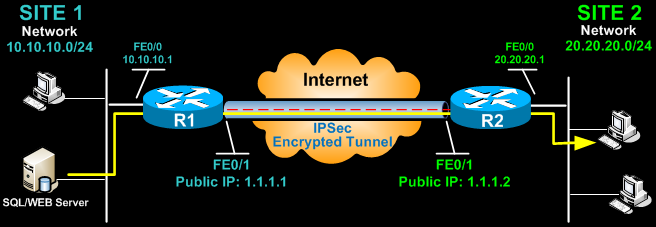
Configuring Site To Site Ipsec Vpn Tunnel Between Cisco Routers The router does this by default. in order to do this, when you define the trustpoint under the crypto map add the chain keyword as shown here: crypto map outside map 1 set trustpoint ios ca chain. if this is not done, then the the tunnel only gets negotiated as long as the asa is the responder. In this article, we configured ipsec vpn on cisco routers. we discussed the requirements for the ipsec vpn. after, we configure phase1 and phase2 on cisco router r1. the same configuration is done on the cisco router r2. you must need the static routable ip address to establish an ipsec tunnel between both the routers. hope you like this article!.
