Configuring Ipsec Site To Site Vpn Tunnels 10.1 and later. the ipsec tunnel configuration allows you to authenticate and or encrypt the data (ip packet) as it traverses the tunnel. ipsec tunnel mode is the default mode. ipsec tunnel mode creates a secure connection between two endpoints by encapsulating packets in an additional ip header. this means, in tunnel mode, the ipsec wraps the. Figure site to site ipsec shows the general layout of this vpn. site to site ipsec ¶ site a¶ start with configuring the tunnel and related settings on the firewall at site a. phase 1¶ to add a new ipsec phase 1: navigate to vpn > ipsec. click add p1. fill in the settings as described below. click save when complete.

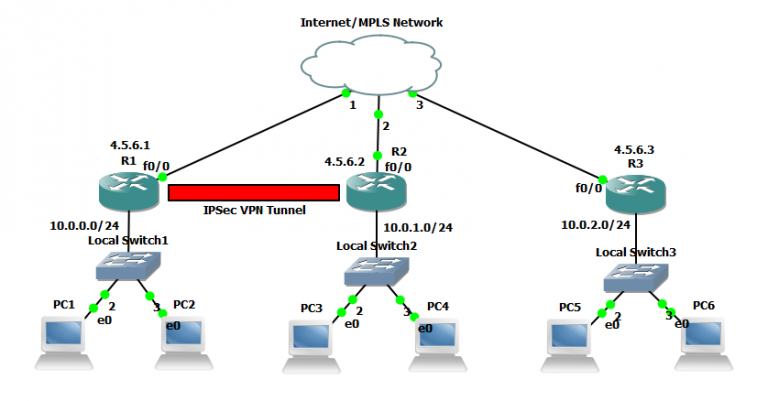
Ipsec Site To Site Vpn Tunnel Configuration On Packettracer To set up site to site vpn: make sure that your ethernet interfaces, virtual routers, and zones are configured properly. for more information, see configure interfaces and zones. create your tunnel interfaces. ideally, put the tunnel interfaces in a separate zone, so that tunneled traffic can use different policy rules. How ipsec works. ipsec involves many component technologies and encryption methods. yet ipsec's operation can be broken down into five main steps: 1. "interesting traffic" initiates the ipsec process. traffic is deemed interesting when the ipsec security policy configured in the ipsec peers starts the ike process.2. ike phase 1. Ipsec can be configured to provide security for a wide range of network topologies, including site to site and remote access connections. in ipsec, you can configure various settings, such as encryption and authentication algorithms and security associations timeouts. one such configuration is the ipsec mode—tunnel mode or transport mode. To help make this an easy to follow exercise, we have split it into two steps that are required to get the site to site ipsec vpn tunnel to work. these steps are: (1) configure isakmp (isakmp phase 1) (2) configure ipsec (isakmp phase 2, acls, crypto map) our example setup is between two branches of a small company, these are site 1 and site 2.

Example Configuring A Site To Site Ipsec Vpn Tunnel Barracuda Ca Ipsec can be configured to provide security for a wide range of network topologies, including site to site and remote access connections. in ipsec, you can configure various settings, such as encryption and authentication algorithms and security associations timeouts. one such configuration is the ipsec mode—tunnel mode or transport mode. To help make this an easy to follow exercise, we have split it into two steps that are required to get the site to site ipsec vpn tunnel to work. these steps are: (1) configure isakmp (isakmp phase 1) (2) configure ipsec (isakmp phase 2, acls, crypto map) our example setup is between two branches of a small company, these are site 1 and site 2. These secure tunnels over the internet public network are encrypted using a number of advanced algorithms to provide confidentiality of data that is transmitted between multiple sites. this chapter explores how to configure routers to create a permanent secure site to site vpn tunnel. encryption will be provided by ipsec in concert with vpn. On both firewalls, configure the ipsec tunnel as described in ipsec site to site vpn example with pre shared keys, with the following exceptions: endpoint a: authentication method: mutual certificate. my identifier: set appropriately to match the certificate for this endpoint. peer identifier:.

Configuring Ipsec Site To Site Vpn Tunnels Vrogue Co These secure tunnels over the internet public network are encrypted using a number of advanced algorithms to provide confidentiality of data that is transmitted between multiple sites. this chapter explores how to configure routers to create a permanent secure site to site vpn tunnel. encryption will be provided by ipsec in concert with vpn. On both firewalls, configure the ipsec tunnel as described in ipsec site to site vpn example with pre shared keys, with the following exceptions: endpoint a: authentication method: mutual certificate. my identifier: set appropriately to match the certificate for this endpoint. peer identifier:.
